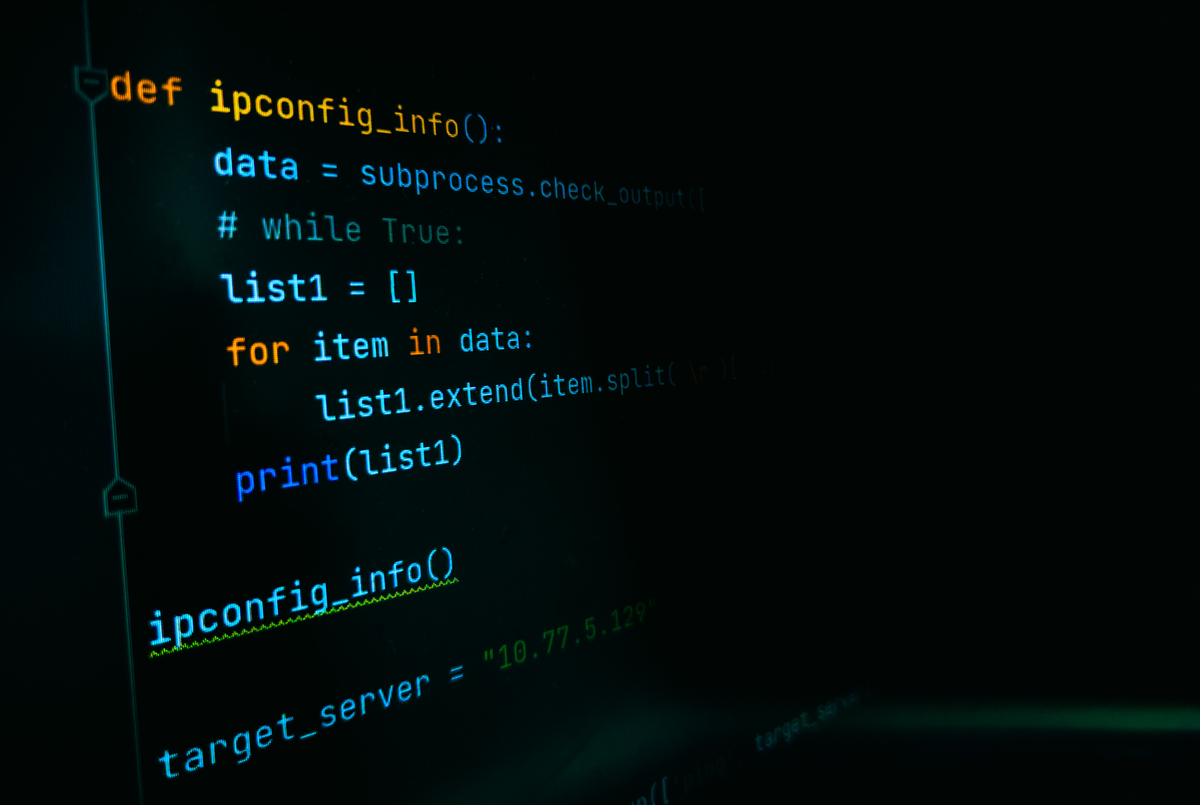
Python GUI Network Security Tool - ARP, ICMP, TCP Detection & Network Scanner
This Python code implements a network security tool with a graphical user interface (GUI) built using the Tkinter library. It provides functionalities for detecting various network attacks such as ARP spoofing, ICMP flooding, TCP attacks, and network scanning. Here's a breakdown of the code and how it works:
MainWindow class:
class MainWindow:
def __init__(self):
self.root = tk.Tk()
self.root.title('Network Security Tool')
self.root.geometry('400x350')
self.arp_button = tk.Button(self.root, text='ARP Detection', command=self.show_arp_page)
self.arp_button.pack()
self.icmp_button = tk.Button(self.root, text='ICMP Flood Detection', command=self.show_icmp_page)
self.icmp_button.pack()
self.tcp_button = tk.Button(self.root, text='TCP Attack Detection', command=lambda: self.show_detection_page('TCP Attack Detection', TcpAttackDetectorPageUI))
self.tcp_button.pack()
self.network_button = tk.Button(self.root, text='Network Scanner', command=self.show_network_page)
self.network_button.pack()
self.root.mainloop()
# Placeholder methods for other detection pages
def show_arp_page(self):
pass
def show_icmp_page(self):
pass
def show_network_page(self):
pass
def show_detection_page(self, title, page_ui_class):
self.master = tk.Toplevel(self.root)
self.master.title(title)
self.master.geometry('400x150')
self.timeout_label = tk.Label(self.master, text='Detection Time (s)')
self.timeout_label.pack()
self.timeout_entry = tk.Entry(self.master)
self.timeout_entry.pack()
self.start_button = tk.Button(self.master, text='Start', command=lambda: self.start_detection(page_ui_class))
self.start_button.pack()
def start_detection(self, page_ui_class):
timeout = int(self.timeout_entry.get())
self.master.withdraw()
page_ui_class(self.master, timeout) # Pass the page UI class to create the detection page
TcpAttackDetectorPageUI class:
class TcpAttackDetectorPageUI:
def __init__(self, master):
self.master = master
self.master.title('TCP Attack Detector')
self.master.geometry('400x150')
self.timeout_label = tk.Label(self.master, text='Detection Time (s)')
self.timeout_label.pack()
self.timeout_entry = tk.Entry(self.master)
self.timeout_entry.pack()
self.start_button = tk.Button(self.master, text='Start', command=self.start_detection)
self.start_button.pack()
def start_detection(self):
timeout = int(self.timeout_entry.get())
self.master.withdraw()
TcpAttackDetectorPage(self.master, timeout) # Create the actual detection page
TcpAttackDetectorPage class (Not shown):
This class would contain the logic for actually performing TCP attack detection. It would likely take the timeout value provided by TcpAttackDetectorPageUI and use network libraries (like scapy) to monitor network traffic for suspicious TCP activity.
Explanation:
- MainWindow:
- Creates the main window with buttons for each detection type.
commandattributes for buttons are set to call respective functions.show_detection_pageis a generic function to create a detection page for different attack types. It takes thetitleandpage_ui_classas parameters.start_detectionis called when the user clicks 'Start' in a detection page.
- TcpAttackDetectorPageUI:
- Creates the GUI elements for the TCP attack detection page (timeout input, start button).
start_detectionmethod gathers the timeout value and creates an instance ofTcpAttackDetectorPage(which would implement the actual detection logic).
- Integration:
show_detection_pageinMainWindowcreates an instance of the relevant UI class (TcpAttackDetectorPageUIin this case).- This UI class handles user interaction (timeout input) and then creates the actual detection page (
TcpAttackDetectorPage) with the provided timeout value.
Key Improvements:
- Unified detection page handling:
show_detection_pageinMainWindowsimplifies creating detection pages for different attack types. - Better code organization: Separates UI (page UI classes) from detection logic (page classes).
- Clearer structure: The code structure is more organized and easier to understand.
Remember: The TcpAttackDetectorPage class (not provided in the example) is where you would implement the actual network monitoring and detection logic for TCP attacks.
This structure makes it easy to add new attack detection types to your tool by simply creating new UI classes and detection classes for them.
原文地址: https://www.cveoy.top/t/topic/jnWv 著作权归作者所有。请勿转载和采集!